Police authorities in Harbin, in northeast China's Heilongjiang Province, said on Tuesday that they are pursuing three operatives affiliated with the U.S. National Security Agency (NSA) over suspected cyberattacks against China.
The Harbin public security bureau said that the three operatives -- Katheryn A. Wilson, Robert J. Snelling, and Stephen W. Johnson -- had been engaged in cyberattacks targeting the Asian Winter Games held in the city in February.
Technical teams also uncovered evidence implicating the University of California and Virginia Tech in the coordinated cyber attacks targeting the Asian Winter Games, authorities stated.
According to public information, the University of California has been recognized as an academic center of excellence in cyber defense education by the NSA and the Department of Homeland Security since 2015. Virginia Tech, one of six senior military colleges in the United States, received funding from the NSA in 2021 to enhance its cyber offense and defense teams.
"Through traceability analysis, we have found that several U.S. universities were involved in attacks on key event systems for the Asian Winter Games. Virginia Tech, a prominent military school, has received funding from various intelligence agencies, including the NSA, the Federal Bureau of Investigation, and the Department of Homeland Security, to strengthen its cyber offense and defense teams and enhance its cyber training facilities. It is also recognized as a 'Cybersecurity Operations Research Center' by the NSA. This weaponization of higher education resources seriously undermines the trust foundation of the international academic community," said Fan Yuan, chairman of DBAPPSecurity Ltd.
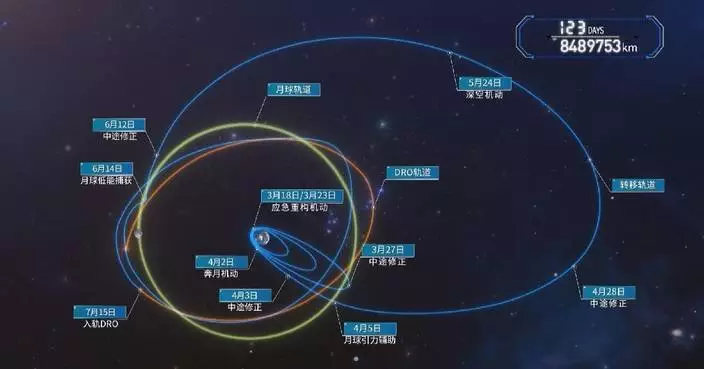
Investigations by Chinese technical teams revealed that the cyberattacks were carried out by the Office of Tailored Access Operations of the NSA. To conceal the origins of its attacks and secure its cyber weapons, the office used multiple affiliated front organizations to purchase IP addresses from various countries and anonymously rented servers located in regions including Europe and Asia.
Investigations revealed that the NSA focused its pre-event cyberattacks on critical systems of the Asian Winter Games, including registration, arrival/departure management, and competition entry platforms, authorities said. These systems, essential for pre-event operations, stored vast amounts of sensitive personal data of individuals associated with the Games.
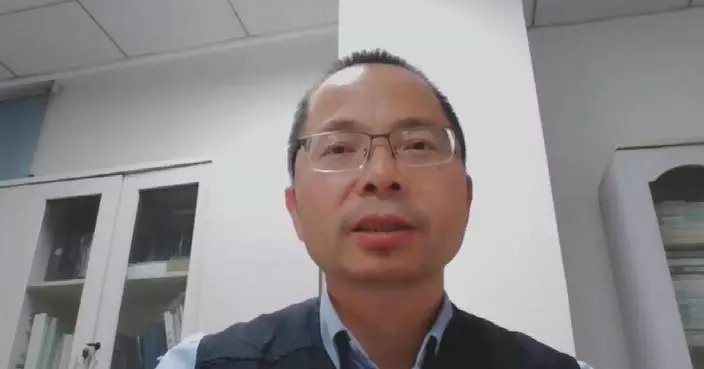
"During the process, we detected and intercepted cyber security attacks from abroad, conducted in-depth analysis and uncovered clues and traces related to critical threats. Throughout the 493-day operation, we performed security inspection and assessments in advance and addressed numerous potential threats. At last, we provided 24/7 monitoring across 23 locations for 15 days," said Xiao Xinguang, chairman of Antiy Labs.
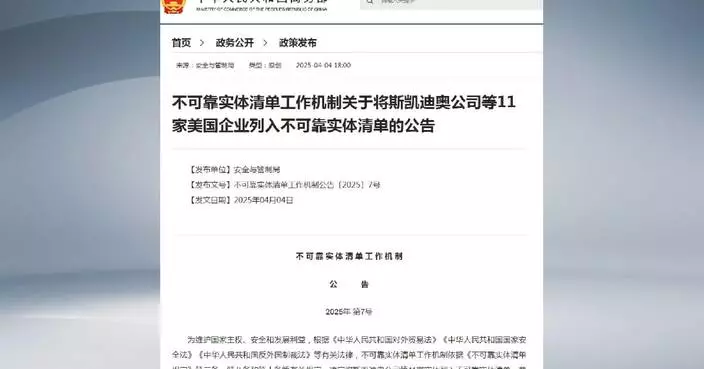
Meanwhile, the NSA launched cyberattacks targeting critical infrastructure sectors in Heilongjiang Province, including energy, transportation, water resources, telecommunications, and defense research institutions, authorities said.
Technical teams also discovered that during the Asian Winter Games, the NSA transmitted unknown encrypted data packets to specific devices running Microsoft Windows operating systems within the province. These packets are suspected to have been attempts to activate or trigger pre-implanted backdoors in the Windows systems, authorities added.

Three US operatives, two US universities involved in cyber attacks against Asian Winter Games: Chinese police